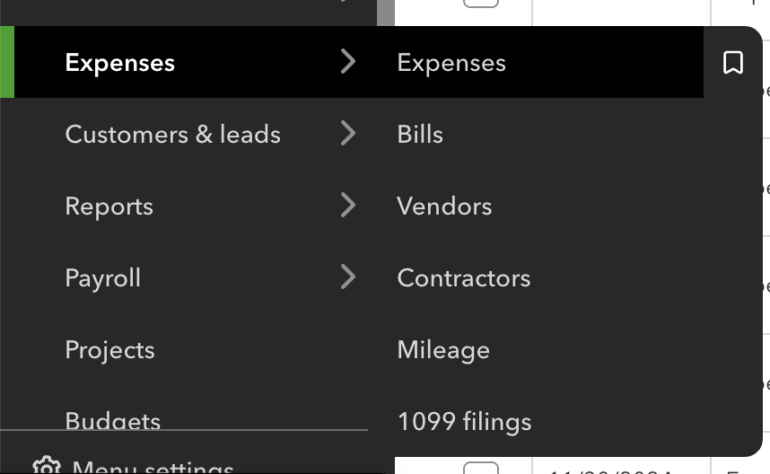
Dashlane fast facts Our rating: 4.4 stars out of 5Pricing: Starts at $4.99 per monthKey features Secure password vault encryption. No recorded data breaches. Well-designed and intuitive user interface. Dashlane has become one of the most popular password managers available — and for good reason. It has top-tier zero-knowledge encryption for its password vault, a ton of convenient usability features, and a very intuitive user-interface. While there are more affordable options available, Dashlane’s feature-packed take on password management makes it one of the best all-around choices in the space. NordPass Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Micro (0-49 Employees), Small (50-249 Employees), Medium (250-999 Employees), Large (1,000-4,999 Employees), Enterprise (5,000+ Employees) Micro, Small, Medium, Large, Enterprise Features Activity Log, Business Admin Panel for user management, Company-wide settings, and more Dashlane Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Micro (0-49 Employees), Small (50-249 Employees), Medium (250-999 Employees), Large (1,000-4,999 Employees), Enterprise (5,000+ Employees) Micro, Small, Medium, Large, Enterprise Features Automated Provisioning ManageEngine ADSelfService Plus Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Any Company Size Any Company Size Features Access Management, Compliance Management, Credential Management, and more Does Dashlane have a free version? Yes, Dashlane has a free plan. However, it is very limited as it only allows for a maximum of 25 passwords stored in user vaults. This makes it an unrealistic option for people looking to use a free password manager long term, especially since I expect the average user to have more than 25 passwords. If you’re looking for a free password manager to use as your main solution, Bitwarden and NordPass are two password managers I recommend, as they both have free plans that offer unlimited password storage. In May 2024, Dashlane also announced that Dashlane Free users who exceeded the 25-password limit would be converted to read-only and would no longer have autofill capabilities unless they upgrade. In my view, this shows that Dashlane is primarily focusing on their paid users and probably have their free plan set up as a test drive tool only. Again, for people looking for a viable, free password manager, there are quality alternatives out there. While this is unfortunate, Dashlane does offer a 30-day trial for its Premium plan. This way, you get a clearer picture of Dashlane’s paid features and user experience, without the limitations that come with the free plan. For more info, we have a Dashlane Free vs Premium feature that dives more extensively into the difference between the two plans. Dashlane Pricing Dashlane has two subscription tiers for individual and business customers, namely Personal and Business. Personal: Personal plans Free plan Premium Friends & Family Price Free $4.99 per month (billed annually) $7.49 per month for up 10 members (billed annually) No. of devices 1 device Unlimited Unlimited Feature differences Maximum of 25 passwords, password sharing Unlimited passwords and passkeys, password sharing, dark web monitor, VPN, real-time phishing alerts All Premium features (VPN only for plan admin) Dashlane’s costs are on the pricier side compared to other password managers. Unfortunately, its Premium plan has raised in price to $4.99 per month compared to its $3.33 monthly price back in 2023. This makes it a fairly pricey option compared to the likes of Bitwarden and Roboform, which have starting plans at $0.83 and $1.66 per month respectively. That’s not to say that Dashlane doesn’t include features to back up its monthly fee. In fact, its starting plan is fully-featured as it includes unlimited device support, unlimited passwords and passkeys, a dark web monitor, and even a built-in VPN. Having a bundled VPN is not something often seen with password managers and a convenient tool that gives Dashlane users additional security. Meanwhile, its Friends and Families plan is also on the expensive end at $7.49 per month. However, it’s important to mention that it’s one of the only password manager family subscriptions that covers 10 people in a single plan. Most other family plans cover 5-6 people, at around $3-6 per user, per month. So in this aspect, I think Dashlane’s Family subscription falls right in the middle compared to other similar offerings. Business: Business plans Standard Business Business Plus Price $20 for 10 users (billed annually) $8 per user, per month (billed annually) $5 per employee, per month (billed annually)Starts at 100 employees No. of devices Unlimited Unlimited Unlimited Feature differences Dark web monitor, password health dashboard, dark web insights All Standard features plus VPN, SSO integration, SCRIM Provisioning, SIEM integration All Business features plus Credential Risk Detection Looking into its business subscriptions, Dashlane’s Standard plan at $20 per month for 10 seats is on trend with other password managers’ similar subscriptions. This plan is ideal for small teams that want a centralized password management solution. If you want a more affordable option, NordPass offers a Teams option of $1.79 per user per month, max 10 users, that’s good for two years. For businesses, Daslane’s Business tier of $8 per seat per month is a good choice, with all Standard plan features plus single-sign on and SIEM integration included. If the higher price tag is out of your budget, Dashlane now offers a Business Plus plan that’s more affordable at $5 per seat, per month, provided your company has a minimum of 100 users. Both plans provide on-demand phone support, real-time phishing alerts, and their built-in VPN. Is Dashlane safe? As it deals with highly sensitive data in passwords, it’s important to know if Dashlane is actually a safe and secure service to use. I’m happy to report that Dashlane checks all of the boxes in terms of security. Dashlane operates on zero-knowledge architecture, which means only the user knows their Master Password and the data stored within their vault. It utilizes AES 256-bit encryption, the industry standard encryption algorithm, to encrypt all passwords and credentials in the vault. It even encrypts all the data