If You Need IVR Compliance, Look for These 6 Features
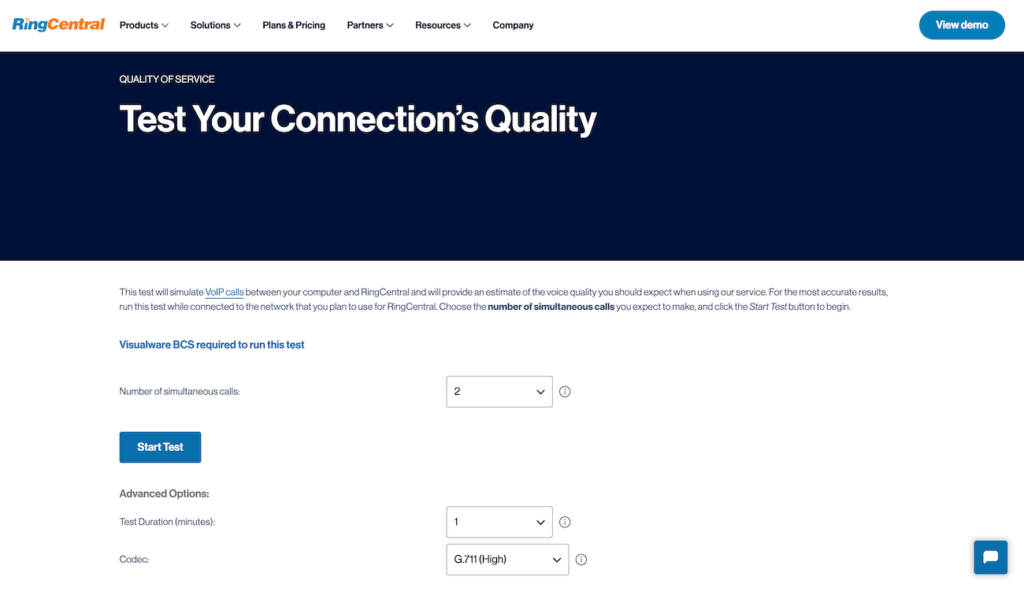
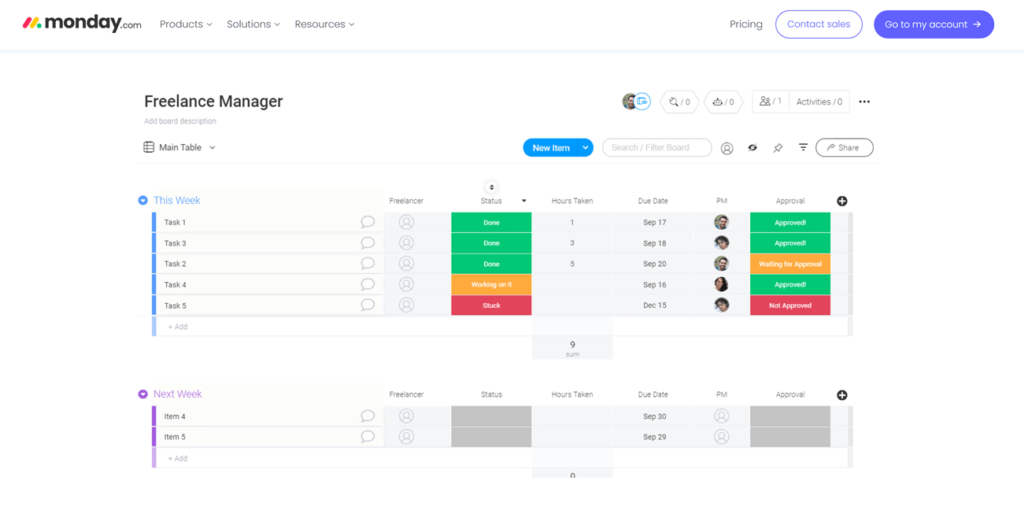
Interactive Voice Response (IVR) is a wonderful tool that helps businesses and their customers get more done in less time. Because people share sensitive data over the system — personal information, patient information, credit card numbers, and so on — IVR compliance is a nontrivial consideration. The most impactful IVR regulations come from the Payment Card Industry Data Security Standard (PCI DSS) and the Telephone Consumer Protection Act (TCPA), but there are others. I’ll cover everything you need to know about IVR compliance in this post and provide tips for finding vendors that offer the features you need to minimize your regulatory burden and simplify compliance. 1 RingCentral RingEx Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Medium (250-999 Employees), Large (1,000-4,999 Employees), Enterprise (5,000+ Employees) Medium, Large, Enterprise Features Hosted PBX, Managed PBX, Remote User Ability, and more 2 Talkroute Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Any Company Size Any Company Size Features Call Management/Monitoring, Call Routing, Mobile Capabilities, and more Managing risk with IVR compliance When it comes to IVRs, several compliance risks are associated with the use of tools that automate functions for boosting revenue — such as collecting payments and scheduling callbacks with prospective or existing customers. The top risks you’ll face as an organization when accepting payments via IVR include the following: Data breaches: When your company accepts card payments and financial information, it becomes a prime target for hackers to steal credit card information. However, if the organization that suffers a data breach is PCI-DSS compliant, its penalties are significantly lowered due to that adherence. Legal action: Data breaches can result in legal action from all affected parties (including credit card companies), which can be very costly and punitive. Complaints and disputes: Improper routing and long call wait times can lead to many unsavory outcomes, especially when money is involved. This dissatisfaction can cause customers to abandon calls in frustration or even switch to competitors. Negative brand perception: One of the main intangible losses a business can face is irreversible damage to its reputation, which is what a data breach caused by lax IVR compliance can inflict. Compliance issues and penalties: Failing to adhere to PCI-DSS standards can result in hefty fines, increased transaction fees, or even the loss of the ability to process credit card payments. The major credit card companies, namely MasterCard, Visa, Discover, and AMEX, formed PCI SSC, and they are the ones who dole out fines for violations. For instance, failure to meet PCI-DSS compliance requirements for over seven months can cost up to $100,000 per month. Additionally, more specific penalties include penalties of $5,000 per month (for low-volume clients) and $10,000 per month (for high-volume clients) if the non-compliance is between 1 to 3 months. If the non-compliance is between 4 to 6 months, the penalties jump to $25,000 per month (for low-volume clients) and $50,000 per month (for high-volume clients). It is important to note that these violations aren’t the same as those imposed by government regulations. With IVR compliance, card brands will impose fines on the payment processor for violations, who, in turn, penalize the responsible merchant. Keep in mind that most risks and penalties can be managed and absorbed relatively easily by institutions like large banks, but if you are a small business, it could lead to bankruptcy. To mitigate the risks, it’s a good idea to incorporate or implement the built-in compliance features of many IVR services. Encryption and data loss prevention measures You must ensure that credit card information is never transmitted across the network in plain text. It is incumbent upon contact centers to mandate that financial data must be encrypted in use, transit, or at rest. Furthermore, point-to-point encryption (P2PE) standards, which are a comprehensive list of security requirements, must be implemented by P2PE providers. Adhere to PCI DSS and other security best practices IVR platforms must implement appropriate data retention policies that won’t jeopardize your customer information. For instance, while handling credit card payments, sensitive authentication data such as CVV/CVV codes cannot be stored after authorization. Moreover, call centers must not store any card data and therefore need to dispose of all stored credit card information. Use an IVR with built-in compliance solutions If you lack the resources or time to build a secure system infrastructure yourself, embracing an existing IVR-compliant payment platform is a viable option. You’ll most likely want to seek a PCI-compliant hosted IVR service provider that implements secure payments — because, apart from taking care of various delivery aspects, one of the advantages is that it removes the need for live agents to handle sensitive card information. In this descoped environment, you eliminate the risk of data breaches caused by mishandled sensitive information. Of course, you’ll also want your solution to be cost-effective and easy to deploy. Check out my guide to IVR pricing if you are unfamiliar with these products — divining the true cost of these systems can be a little confusing. In any case, finding the right IVR provider for you comes down to investigating the following six prospective features. SEE: Learn why you should use a hosted IVR rather than hosting your own. Six important features for IVR compliance 1. Compliance certifications I thought about not including this on the list because it’s common sense — but this is a post about compliance, so I am not taking any chances. It’s crucial to confirm the provider holds the necessary compliance certifications to ensure secure and lawful operations. Key certifications to look for include: PCI-DSS (Payment Card Industry Data Security Standard). ISO 27001 (International Organization for Standardization – Information Security Management). SOC 2 (System and Organization Controls 2). GDPR (General Data Protection Regulation). CCPA (California Consumer Privacy Act). For healthcare-related use cases, HIPAA (Health Insurance Portability and Accountability Act) compliance is especially important. The business phone service or IVR provider must be prepared to sign a Business Associate Agreement
If You Need IVR Compliance, Look for These 6 Features Read More »