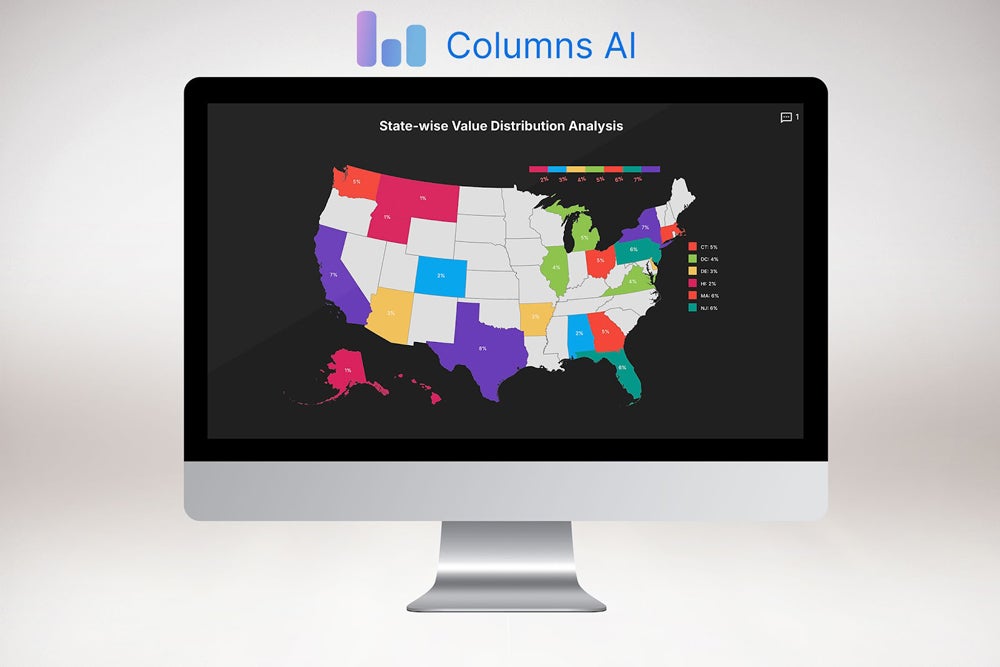
Security experts advise creating strong, complex passwords to protect our online accounts and data from savvy cybercriminals. And “complex” typically means using lowercase and uppercase characters, numbers, and even special symbols. But, complexity by itself can still open your password to cracking if it doesn’t contain enough characters, according to research by security firm Hive Systems. In this article, we look into how long it would take for hackers to crack different types of passwords and what you can do to make them more secure. NordPass Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Micro (0-49 Employees), Small (50-249 Employees), Medium (250-999 Employees), Large (1,000-4,999 Employees), Enterprise (5,000+ Employees) Micro, Small, Medium, Large, Enterprise Features Activity Log, Business Admin Panel for user management, Company-wide settings, and more Dashlane Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Micro (0-49 Employees), Small (50-249 Employees), Medium (250-999 Employees), Large (1,000-4,999 Employees), Enterprise (5,000+ Employees) Micro, Small, Medium, Large, Enterprise Features Automated Provisioning Scalefusion Single Sign-On Employees per Company Size Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+) Any Company Size Any Company Size Features Access Management, Conditional Access, Credential Management, and more How long does it take to crack a password? In their 2024 Hive Systems Password Table report, Hive found that a complex, eight-character password that contains numbers, symbols, and both upper and lowercase letters will take seven years to crack — if an attacker were to use a top-of-the-line 12 x RTX 4090 graphics card. In comparison, a five-character password with only upper and lowercase letters can be cracked in two minutes. Further, Hive says that a four-character password with only lowercase letters can be hacked instantly, while a five-character password with both upper and lowercase letters can be hacked in three seconds. The 2024 Hive Systems Password Table. Image: Hive Systems In my view, this shows how crucial it is to apply password best practices, such as using a mix of letters, symbols, and numbers, whenever possible. This is especially so since, given the stark contrast in the amount of time passwords could be cracked depending on their complexity. On the plus side, even simpler passwords with a greater number of characters are less vulnerable to cracking in a short amount of time, according to Hive’s research. For example, a 10-character password made up of numbers would take one hour to crack. Meanwhile, upping that number-only password to 18 characters will increase the time frame to 11,000 years. Looking into words versus numbers, Hive’s data shows that passphrases win over more traditional passwords. An 18-character password with only numbers would require 11,000 years to crack, but one with the same number of characters using lowercase letters would take 350 billion years to crack. This piece of data shows why passphrases, which use a long string of real but random words, can be more secure than a complex but short password. Hive’s report shows that passphrases with a mix of 18 uppercase and lowercase letters, numbers, and symbols are the most difficult to brute force. What tools do hackers use to crack your passwords? A hacker aiming to crack complex yet short passwords quickly enough would need the latest and most advanced graphics processing technology. The more powerful the graphics processing unit, the faster it can perform such tasks as mining cryptocurrencies and cracking passwords. With these GPUs, hackers can initiate brute-force attacks and use password-cracking software to guess your passwords and other credentials. Brute force attacks involve using GPUs and machine-powered trial and error in an attempt to get the right combination of characters, numbers, and symbols and, eventually, crack a user’s password. For example, one of the top GPUs around today is Nvidia’s GeForce RTX 4090, a product that starts at $1,599. But even less powerful and less expensive GPUs can crack passwords of a small length and low complexity in a relatively short amount of time. Hackers who don’t have the latest and greatest graphics processing on their computers can easily turn to the cloud, according to Hive. By renting computer and graphics hardware through Amazon AWS and other cloud providers, a cybercriminal can tap into multiple virtual instances of a powerful GPU to perform password cracking at a fairly low cost. Plus, the advances in AI have given hackers another type of tool to crack passwords more quickly and efficiently. An April 2023 report from Home Security Heroes that analyzed 15,600,000 common passwords discovered that by using AI, hackers could crack 81% of them in less than a month, 71% in less than a day, 65% in less than an hour, and 51% in less than a minute. SEE: Securing Linux Policy (TechRepublic Premium) How to protect yourself and your organization from password cracking Due to the progress in graphics and AI technology, most types of passwords require less time to crack than they did only two years ago. For example, a seven-character password with letters, numbers, and symbols would take seven minutes to crack in 2020 but only four seconds in 2023. Given these technological advances, how can you and your organization better secure your password-protected accounts and data? Here are a few tips. Try using a passphrase instead of a password A passphrase is a long string of often random words. Passphrases are often more secure than passwords and are usually easier to remember. Examples of this would be something like “Sunset-cola-Mouse!” or “GatePen2BoxerRose”. If you go the passphrase route, there are a few things to remember: Make sure it’s at least 10-15 characters or more. Avoid using common phrases or song lyrics. Choose a passphrase that’s memorable to you. Add in some numbers and symbols to your phrases. For a more in-depth tutorial, check out our What is a Passphrase? guide here. Use a mix of numbers, symbols, uppercase, and lowercase letters at the same time One of the main takeaways from the Hive Systems report is the significant